CASE STUDY
Supercharge Kubernetes RBAC with Okta
Improving Kubernetes access control with identity-driven RBAC, Okta integration, and safer multi-team cluster access.
Kubernetes · RBAC · Okta · Security · Identity Access
Introduction
Kubernetes is a powerful platform for orchestrating applications at scale, but managing secure access to cluster resources becomes increasingly complex as teams grow.
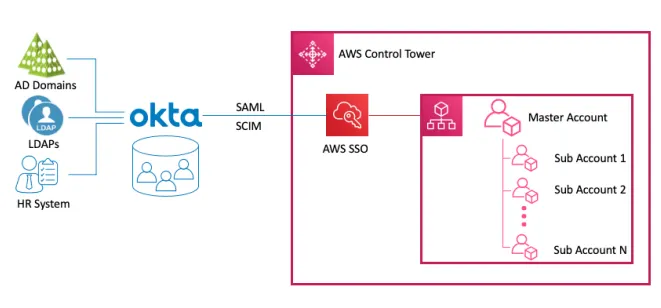
To address this, I implemented an identity-first RBAC approach by integrating Kubernetes with Okta. This made access control easier to manage, more auditable, and safer across engineering teams.

The Challenge of Traditional Kubernetes Access Management
In many Kubernetes environments, access control relies on static credentials and manually maintained role bindings. Over time, this creates security and operational overhead.
Core issues we faced:
- Static kubeconfig credentials are difficult to rotate and easy to misuse.
- No centralized identity source means user lifecycle events are inconsistently enforced.
- Manual role updates are error-prone and slow in fast-moving teams.
- Poor auditability makes it difficult to answer who has access to what and why.
Without centralized identity and policy alignment, cluster access can drift from least-privilege standards.
How to Integrate Kubernetes RBAC with Okta
The implementation combined Kubernetes RBAC primitives with Okta groups and OIDC authentication.
1. Create Okta Groups by Access Scope
I created group structures in Okta to map directly to Kubernetes access patterns, for example:
- `k8s-admins`
- `k8s-developers`
- `k8s-readonly`
This allowed access ownership to stay with identity governance while Kubernetes consumed group claims.
2. Define Kubernetes Roles and RoleBindings
For each access scope, I defined Kubernetes `Role` / `ClusterRole` objects and mapped them with `RoleBinding` / `ClusterRoleBinding`.
Typical workflow:
kubectl apply -f role.yaml
kubectl apply -f rolebinding.yamlThe role definition scoped actions to required resources only, and the binding linked those permissions to the matching Okta group.
3. Configure OIDC Authentication in Kubernetes and kubectl
I configured Kubernetes authentication to trust Okta as the OIDC identity provider and used OIDC-based login for client access.
Representative client setup pattern:
kubectl config set-credentials okta-user \
--exec-api-version=client.authentication.k8s.io/v1beta1 \
--exec-command=kubectl \
--exec-arg=oidc-login \
--exec-arg=get-token \
--exec-arg=--oidc-issuer-url=https://<okta-domain>/oauth2/default \
--exec-arg=--oidc-client-id=<client-id> \
--exec-arg=--oidc-extra-scope=groupsThis ensured authenticated sessions produced identity tokens that included group claims used by RBAC bindings.
4. Validate Access with Group-Based Tests
I validated the setup by testing access behavior across user personas:
- Admin users with elevated permissions
- Developer users with namespace-scoped privileges
- Read-only users with view-only access
This confirmed policy boundaries worked as expected.
Benefits of Using Okta for Kubernetes RBAC
The integration delivered practical security and operational improvements:
- Centralized access management through one identity platform
- Stronger security via OIDC and group-based authorization
- Scalability for onboarding/offboarding across many teams
- Improved compliance with clearer audit trails
- Consistent access policy enforcement across clusters
- Lower operational overhead for access administration
- Faster incident response when revoking or updating access
Technical Issues and How to Fix Them
During implementation, several issues surfaced and were resolved:
- OIDC misconfiguration: Incorrect issuer URLs, client settings, or claim mappings were corrected by aligning Kubernetes OIDC settings with Okta app configuration and verifying token claims.
- Role binding mismatches: Okta group names and RBAC subjects were standardized with consistent naming conventions and recurring binding validation.
- Token/session failures: Session handling and client auth tooling checks were improved to reduce expiry-related issues.
- Permission debugging complexity: Deterministic policy tests and clearer role boundary documentation improved troubleshooting.
Benefits and Drawbacks
A realistic implementation view includes trade-offs.
Benefits
- Security posture improves through identity-backed least privilege
- Access lifecycle management becomes faster and cleaner
- Governance and audits are significantly easier
Drawbacks
- Initial setup complexity is non-trivial
- Teams need OIDC/RBAC operational familiarity
- Identity availability and integration health become critical dependencies
Conclusion
Integrating Kubernetes RBAC with Okta is a high-leverage upgrade for organizations managing multi-team clusters.
By combining centralized identity, group-based authorization, and policy-driven RBAC, teams gain better security, stronger governance, and more maintainable access operations.
For organizations scaling Kubernetes adoption, this pattern creates a safer and more operationally sustainable access model.